How to Uninstall VeraCrypt from Windows Computer?
Are you looking to uninstall VeraCrypt from your Windows computer? Are you seeking for an easy method to get rid of all VeraCrypt leftovers completely? Or are you trying to remove VeraCrypt but don’t know from where to start? At there, you’ll get these questions answered.

VeraCrypt Overview
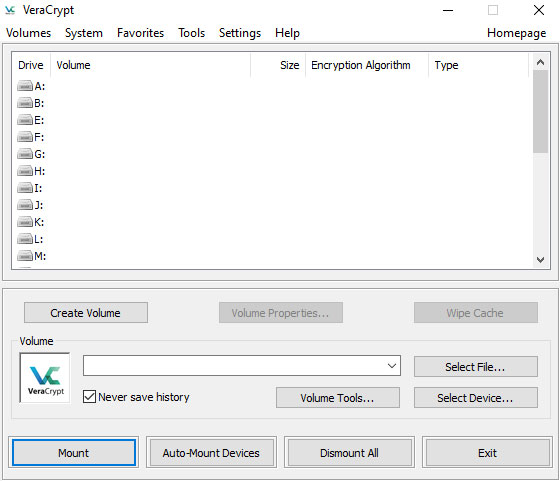
VeraCrypt is a sort of disk-encryption software concentrates on protecting users’ disks from attacks. Whether you are working on Windows computer, Mac OSX, or Linux, VeraCrypt provides you a series of versions of operating systems. With it, you can easily build a virtual encrypted disk within a file, encrypt your hard drive, USB flash drive and other storage devices, or an entire partition securely. So, if you wish to encrypt your hard drive or the entire computer, the VeraCrypt software caters to your needs.
Complete Guide to Uninstall VeraCrypt from Windows
We’ll introduce two methods regarding how to uninstall VeraCrypt from your Windows based computer. The first method will tell you how you can uninstall a program on your own. The second method will help you know a faster and easier solution to remove VeraCrypt and any unwanted programs thoroughly. If you want to know more about the manual steps to uninstall VeraCrypt, refer to the first method. However, if you are wishing to use an automatic uninstaller tool to help you troubleshoot all the issues of cleaning out VeraCrypt, then you can skip the first method and go and try the second method directly.
Method 1: Remove VeraCrypt in Manual Way
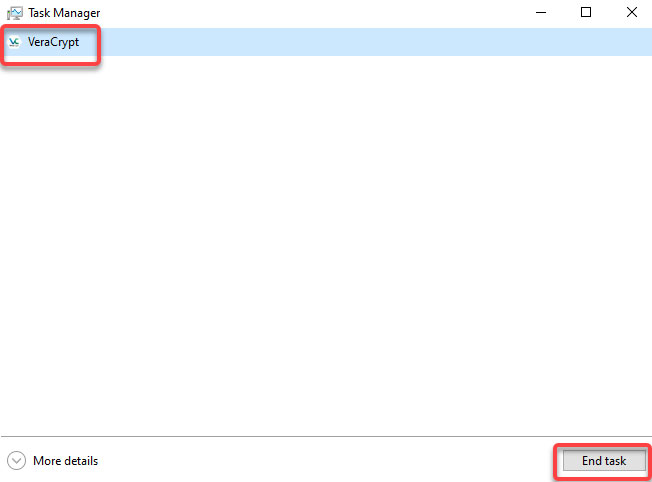
1. Before we start removing the VeraCrypt program, we should make sure the program is closed and there isn’t any activity running in the background. So we will start with Task Manger. Right-click the Start menu and click Task Manager from the pop-up menu options. In the Task Manager, click CPU tab > select the VeraCrypt program and click Close or End Task.
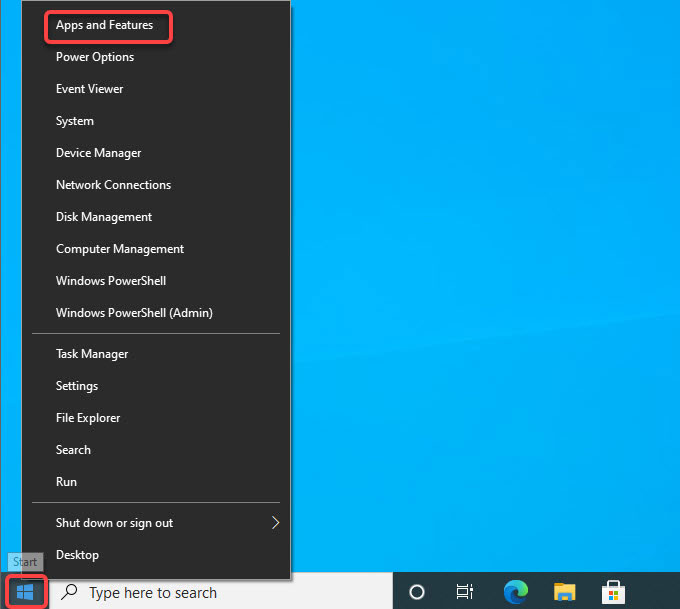
2. Right-click the Start menu to open Programs and Features or Apps and Features.
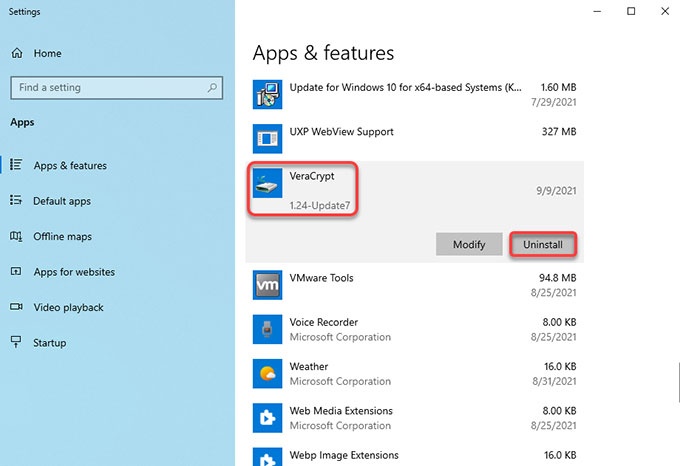
3. In the Programs and Features window, click or right-click the VeraCrypt program that you are looking to uninstall > click Uninstall.
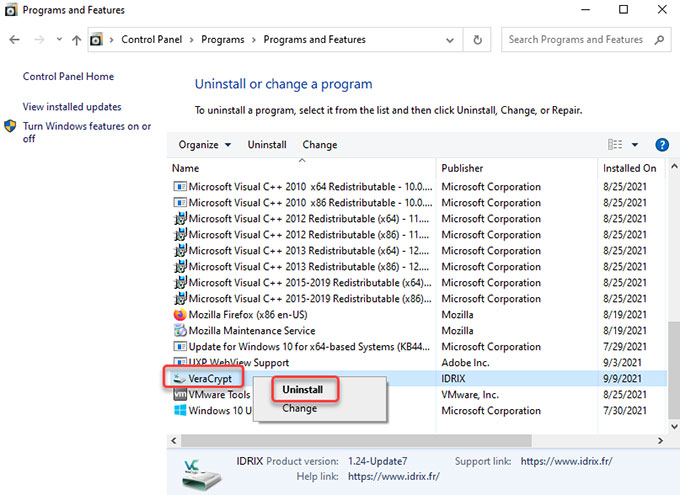
However, if you are on Windows 10, you can see a different interface that is called Apps & Features. Click the VeraCrypt program > click Uninstall.
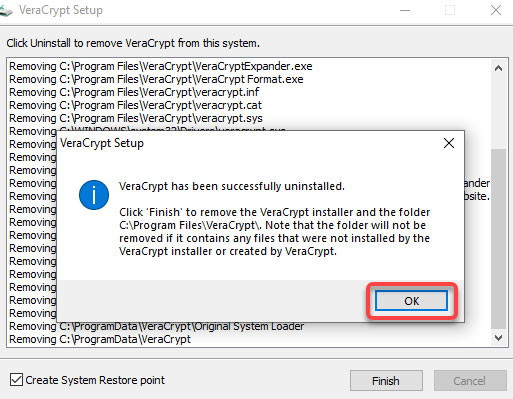
4. Click Yes to make it certain that you would like to uninstall VeraCrypt right now. You then just need to follow the pop-up uninstall wizard to get the VeraCrypt removed from your PC.
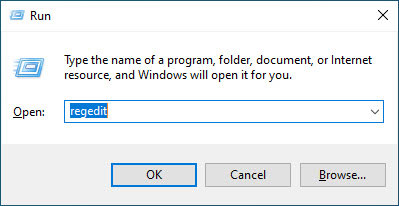
5. Next, you still need to find and delete all leftovers associated with the target VeraCrypt program. And we will start with opening Registry Editor. Press Windows + R keys together to open Run, enter regegit in the open box and press Enter key.
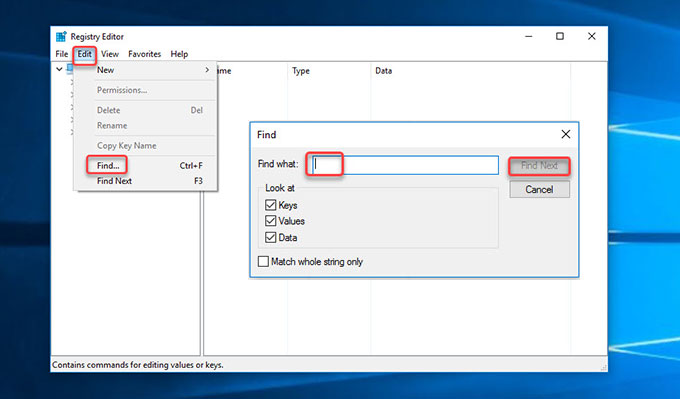
6. From the Registry Editor window, click Edit > click Find… fill in VeraCrypt > click Find Next. From the search result, find and delete files relevant with the VeraCrypt program.
Method 2: Uninstall VeraCrypt in Bloatware Uninstaller
1. Launch Bloatware Uninstaller >click the VeraCrypt program that you are ready to uninstall> click Run Analysis.

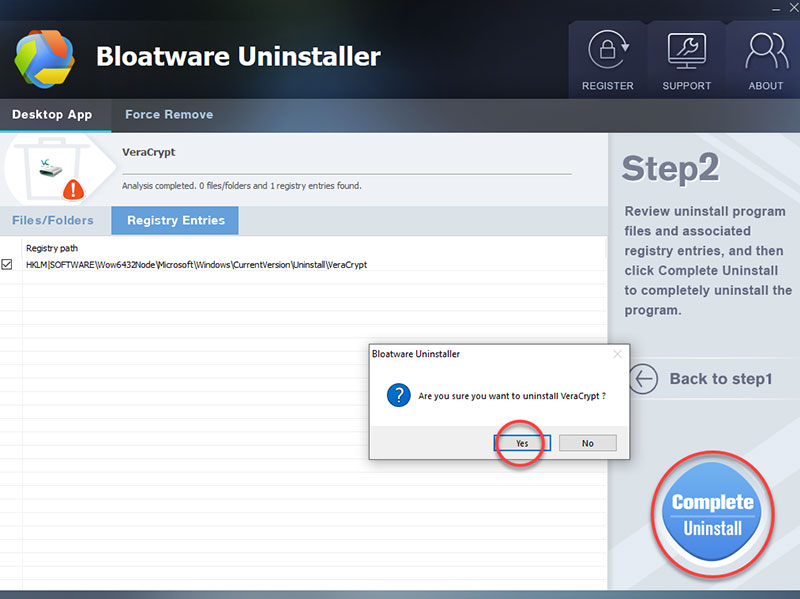
2. Click Complete Uninstall > click Yes to confirm that you would like to uninstall VeraCrypt from your PC right now.
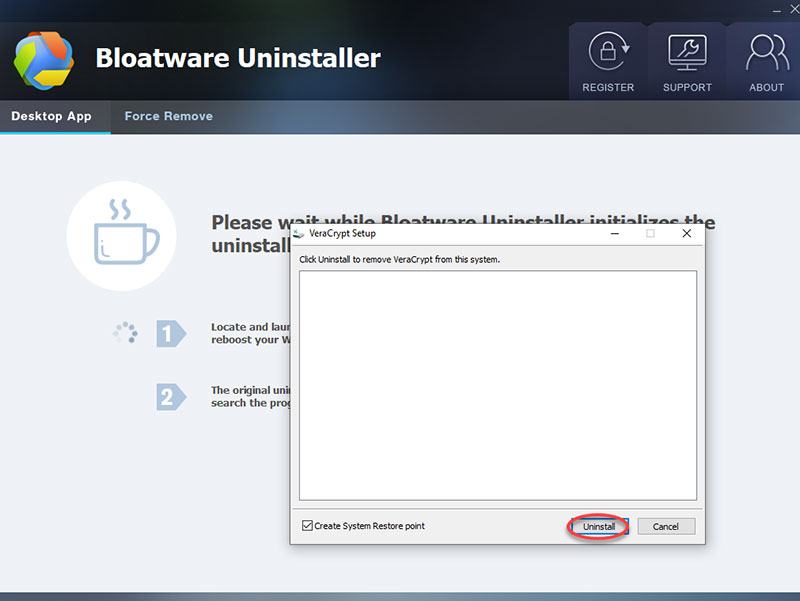
3. Click Uninstall to continue removing the VeraCrypt program from this system.
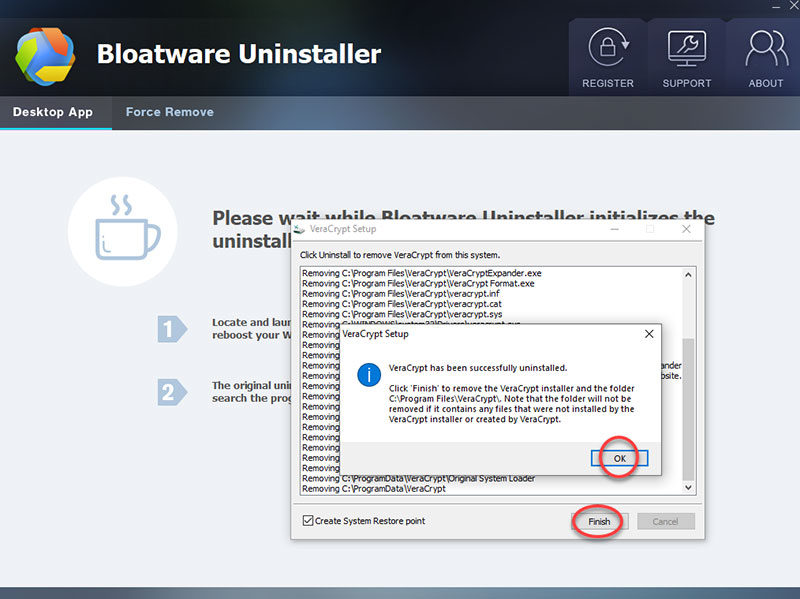
4. VeraCrypt has been successfully uninstalled. Click OK > click Finish to quit the VeraCrypt setup wizard.
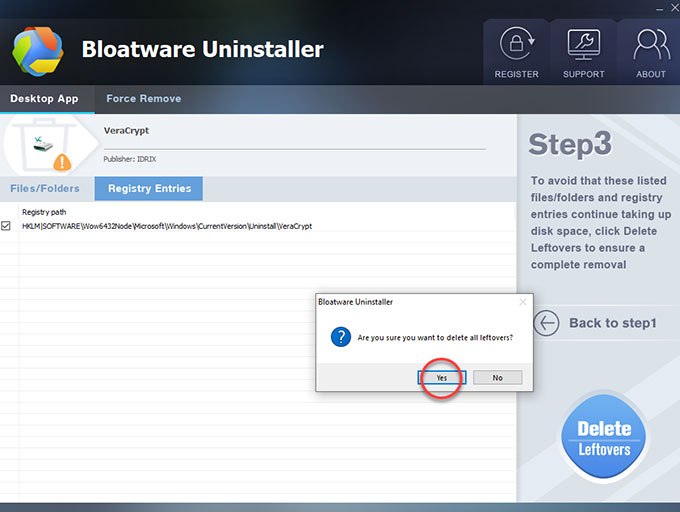
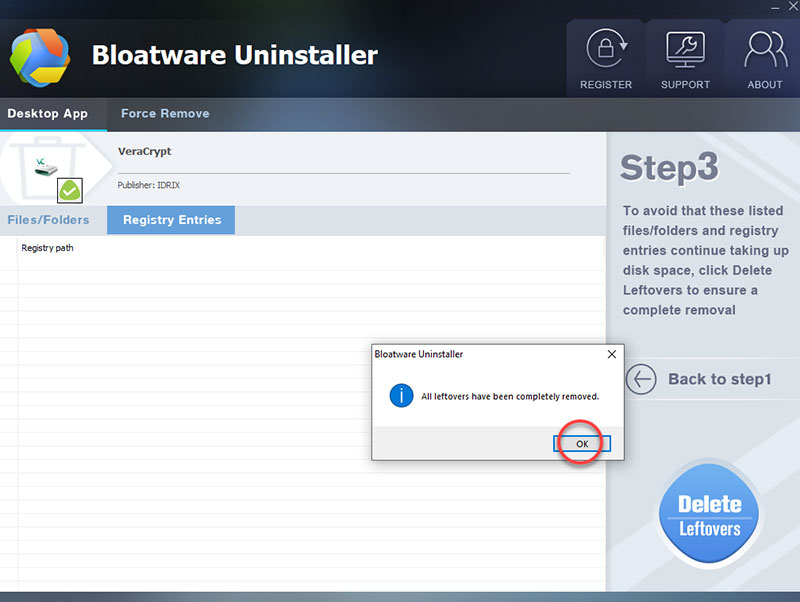
5. Click Scan Leftovers to clean out leftovers from your computer. Click Delete Leftovers > click Yes to make sure that you want to delete all leftovers related with the VeraCrypt program.
6. All leftovers have been completely removed, click OK and click Back to step 1 to check. And then Restart your computer to apply the change.
Also: Refer to a simple video guide regarding how to uninstall VeraCrypt with Bloatware Uninstaller.
VeraCrypt Protects PC from Physical Attacks
Physical attacks on disk encryption are everywhere, we’ll speak about many different physical attacks to give us an idea of the sort of threats that are out there. Many of these types of threats will help circumvent encryption or help obtain the secret key. These included hardware, key loggers, retro reflectors, firmware rookies, as well as simply observing a person through a hidden camera typing in the password that unlocks the encrypted disk. There are all forms of physical attacks to easily defeat encryption by simply obtaining the key with encryption, you have to attack the weakest links and installing a camera to watch you type in the password is much easier than trying to brute force the password. The main mitigation to physical attacks is by whatever method possible. Don’t allow your adversary to touch your device or even visit locations where you use your device. This obviously isn’t always possible, but it should be your first line of defense. If the consequences are high, acquire your device is a secure and anonymous way. Make sure it is fully switched off, not in harmony or sleep, fully switched off, lock it away, conceal it. Don’t leave the house without it. Your device could even be intercepted and modified before you even get it. Which is why open source hardware is becoming more popular.
As we have mentioned critically, once you enter your password or use your token or your key is in some way entered and your drive is decrypted, the decryption key is then in memory. It has to be so you can view your files. Anyone who can get access to the memory can determine your key. There are many physical attacks to do this.
There are a whole host of other physical attacks. They could replace the device or hard drive with a similar one with a hacked bootloader. To capture the key, they can install hardware, key loggers, a boss mastering device, capturing memory firmware root kits, or install any other malicious hardware, allowing the attackers to capture unencrypted data, including encryption keys and passwords. Till now, you may understand why a lot of people choose to use a disk encryption software to protect their devices from attacks. VeraCrypt just is one of the optimal disk encryption software that can help encrypt and protect your hard drive in real-time.
Warm tips: If you want to use the professional Bloatware Uninstaller to uninstall VeraCrypt with a few clicks, simply click the download button below to get started immediately.
- Encryption Software
- 13 Sep 2021

